peterschreiber.media | Getty Photographs
A Chinese language authorities hacking group has acquired a big foothold inside important infrastructure environments all through the US and Guam and is stealing community credentials and delicate information whereas remaining largely undetectable, Microsoft and governments from the US and 4 different international locations mentioned on Wednesday.
The group, tracked by Microsoft beneath the title Volt Storm, has been lively for a minimum of two years with a concentrate on espionage and knowledge gathering for the Folks’s Republic of China, Microsoft mentioned. To stay stealthy, the hackers use instruments already put in or constructed into contaminated gadgets which are manually managed by the attackers slightly than being automated, a method generally known as “dwelling off the land.” Along with being revealed by Microsoft, the marketing campaign was additionally documented in an advisory collectively printed by:
• US Cybersecurity and Infrastructure Safety Company (CISA)
• US Federal Bureau of Investigation (FBI)
• Australian Cyber Safety Centre (ACSC)
• Canadian Centre for Cyber Safety (CCCS)
• New Zealand Nationwide Cyber Safety Centre (NCSC-NZ)
• United Kingdom Nationwide Cyber Safety Centre (NCSC-UK)
Moreover the living-off-the-land approach, the hackers additional obscured their exercise through the use of compromised house and small workplace routers as intermediate infrastructure that enables communications with contaminated computer systems to emanate from ISPs which are native to the geographic space. In Microsoft’s advisory, researchers wrote:
To attain their goal, the menace actor places robust emphasis on stealth on this marketing campaign, relying virtually solely on living-off-the-land strategies and hands-on-keyboard exercise. They situation instructions through the command line to (1) gather information, together with credentials from native and community techniques, (2) put the information into an archive file to stage it for exfiltration, after which (3) use the stolen legitimate credentials to take care of persistence. As well as, Volt Storm tries to mix into regular community exercise by routing visitors by compromised small workplace and residential workplace (SOHO) community tools, together with routers, firewalls, and VPN {hardware}. They’ve additionally been noticed utilizing customized variations of open-source instruments to ascertain a command and management (C2) channel over proxy to additional keep beneath the radar.
The Microsoft researchers mentioned that the marketing campaign is probably going designed to develop capabilities for “disrupting important communications infrastructure between the US and Asia area throughout future crises.” Guam is necessary to the US navy due to its Pacific ports and the air base it offers. As tensions over Taiwan have simmered, the strategic significance of Guam has grow to be a focus.
Commercial
The preliminary entry level for the Volt Storm compromises is thru Web-facing Fortinet FortiGuard gadgets, which in recent times have proved to be a serious beachhead for infecting networks. By exploiting vulnerabilities in FortiGuard gadgets that admins have uncared for to patch, the hackers extract credentials to a community’s Energetic Listing, which shops usernames, password hashes, and different delicate data for all different accounts. The hackers then use that information to contaminate different gadgets on the community.
“Volt Storm proxies all its community visitors to its targets by compromised SOHO community edge gadgets (together with routers),” Microsoft researchers wrote. “Microsoft has confirmed that lots of the gadgets, which embody these manufactured by ASUS, Cisco, D-Hyperlink, NETGEAR, and Zyxel, permit the proprietor to reveal HTTP or SSH administration interfaces to the Web.”
The rest of the advisory principally outlines indicators of compromise that admins can use to find out if their networks have been contaminated.
Microsoft researchers wrote:
Most often, Volt Storm accesses compromised techniques by signing in with legitimate credentials, the identical means approved customers do. Nonetheless, in a small variety of instances, Microsoft has noticed Volt Storm operators creating proxies on compromised techniques to facilitate entry. They accomplish this with the built-in netsh portproxy command.
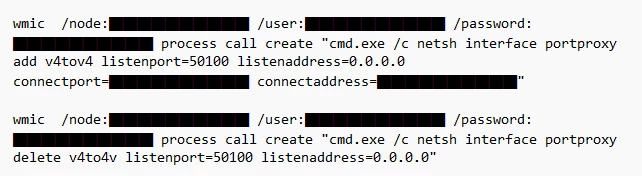
Volt Storm instructions creating and later deleting a port proxy on a compromised system
In uncommon instances, additionally they use customized variations of open-source instruments Impacket and Quick Reverse Proxy (FRP) to ascertain a C2 channel over proxy.
Compromised organizations will observe C2 entry within the type of profitable sign-ins from uncommon IP addresses. The identical person account used for these sign-ins could also be linked to command-line exercise conducting additional credential entry. Microsoft will proceed to observe Volt Storm and monitor adjustments of their exercise and tooling.
Among the many industries affected are communications, manufacturing, utility, transportation, development, maritime, authorities, data know-how, and training. The advisories present steering for disinfecting any networks which have been compromised.
Originally posted 2023-05-25 03:45:53.